A platform to support your intelligence tasks
Tap into all the sources you need in one place, extract critical information at scale and deliver meaningful insights with confidence.
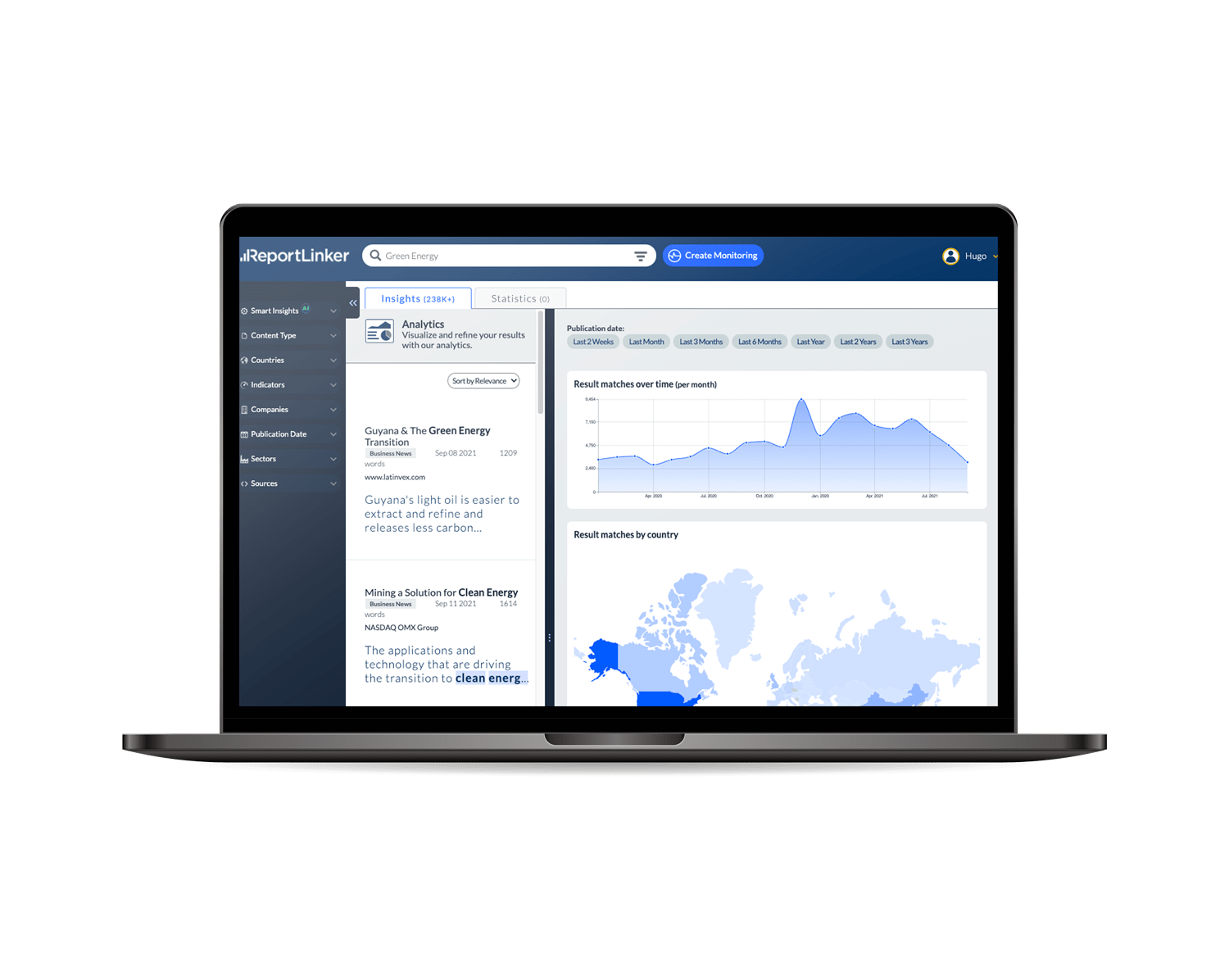
Gather all your intelligence in ONE place
Our AI tracks critical insights from millions of news, company filings, government records, presentations and market research reports, internally and externally.
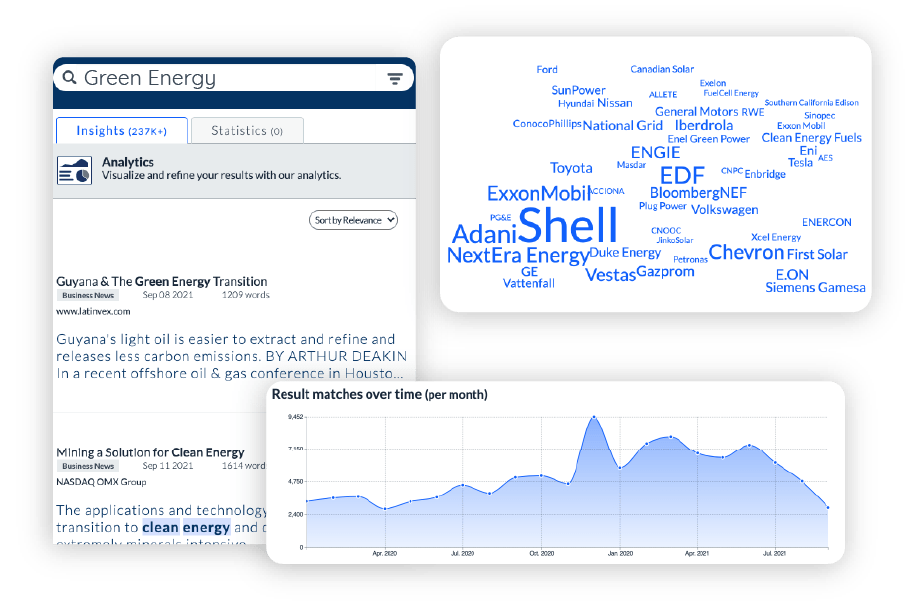
Extract Insights, automate intelligence
Accelerate analysis and automate your tasks with deep learning models trained to surface key intelligence and visual analytics.
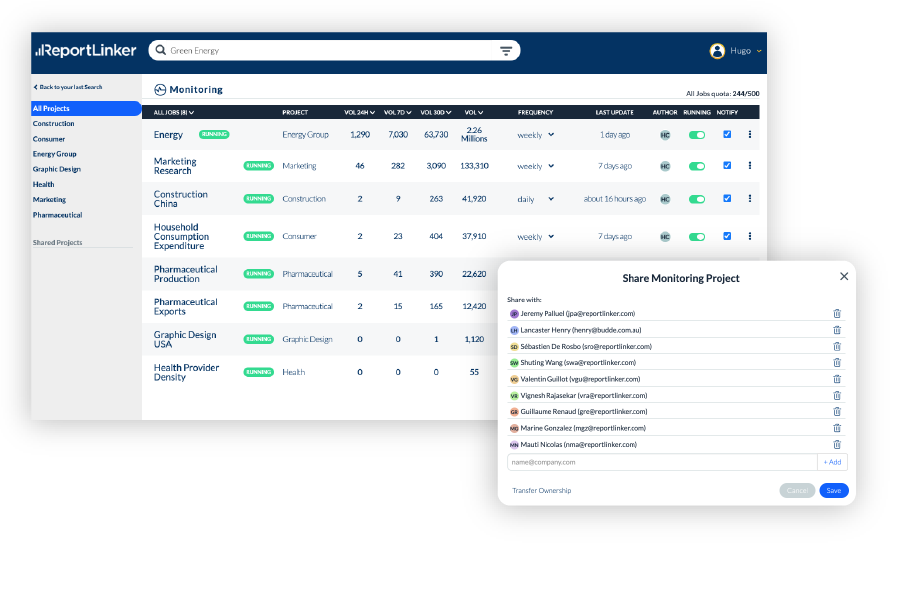
Share your knowledge
Accelerate your answers to stakeholders with a workflow designed to streamline your deliverables.
Create, share and generate better engagement with your team.
Extract insights to spreadsheet
Extract and normalize data (named entity, numbers, facts, topics) from large volumes of textual information.
Get curated, normalized and enriched data points, populated from millions of articles, stories, government and company fillings.